Web Application Development for Healthcare
Healthcare application development is the practice of building web applications for healthcare organizations with HIPAA compliance engineered into every architecture decision - from data storage encryption and role-based access control to audit logging and secure data transmission. Protected health information (PHI) is individually identifiable health data that HIPAA regulates, so healthcare applications cannot treat security as a late-stage checklist. Compliance changes database design, authentication, API security, hosting, logging, vendor selection, and every integration point that touches patient data.
HIPAA is not a feature added at the end of development. HHS Office for Civil Rights explains that the HIPAA Security Rule requires administrative, physical, and technical safeguards for electronic protected health information, and the technical layer directly affects how software is designed. A development team that treats HIPAA compliance as a checklist builds a different application than a team that treats HIPAA-compliant architecture as the foundation.
Kavara builds healthcare application development projects for mid-market healthcare organizations that need production systems, not generic software with medical labels. The four most common application types are patient portals, EHR integration platforms, telehealth applications, and clinical workflow tools. Each healthcare application type serves a different operational need, but all four must protect PHI through encrypted storage, access controls, audit trails, secure transmission, and business associate agreement coverage where required. A business associate agreement is the HIPAA contract for vendors that handle PHI.
Kavara's healthcare development services help regional health systems, specialty clinics, behavioral health organizations, health tech startups, and medical device companies build, launch, and comply with healthcare software requirements. We scope compliance during discovery, design access control before development, verify PHI boundaries during QA, and deploy only after the infrastructure, vendors, and monitoring model match the healthcare risk profile.
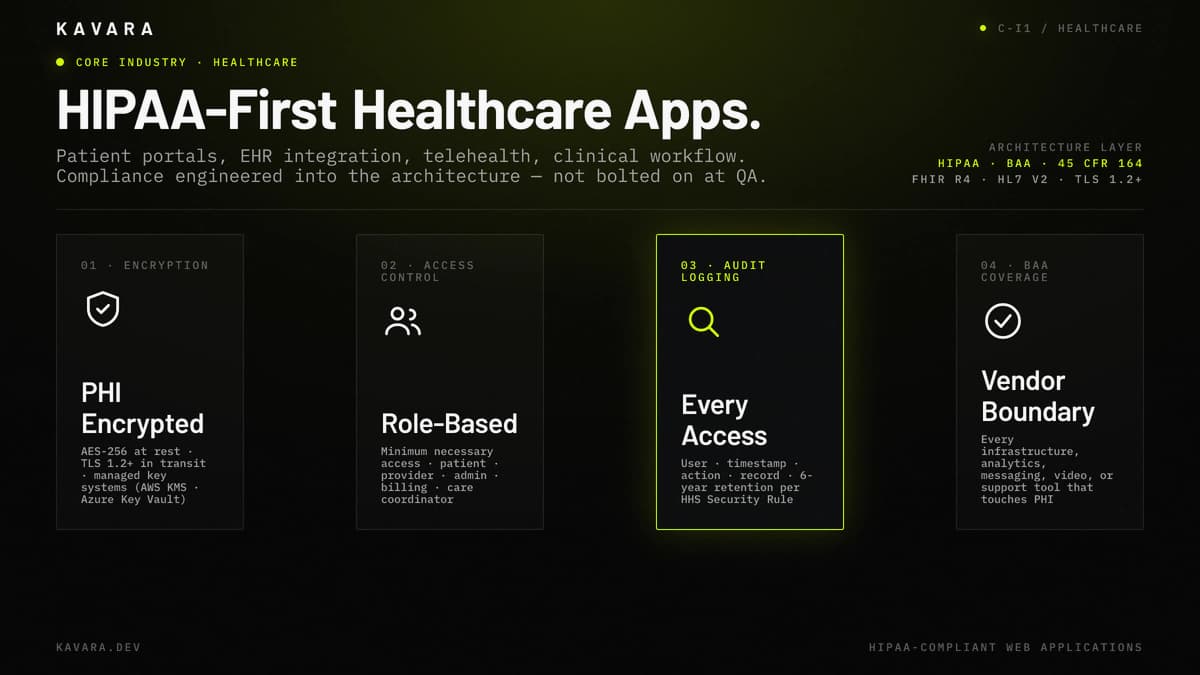
The diagram below maps the four HIPAA architecture pillars that anchor every healthcare application we build — encryption, role-based access control, audit logging, and BAA-covered cloud.
What Is Healthcare Application Development
Healthcare application development is a compliance-first form of web application development that builds patient-facing, provider-facing, and operational software around protected health information, clinical workflows, and healthcare interoperability requirements. Healthcare development differs from general web application development because every architecture decision passes through a HIPAA compliance filter before implementation.
The same engineering principles still apply. Healthcare applications may use React frontends, Node.js or Python backends, PostgreSQL databases, cloud hosting, REST APIs, and modern CI/CD workflows. The difference is the compliance layer around those choices. Database design must account for PHI encryption at rest and in transit. Authentication must account for stronger identity verification, session timeout, and minimum necessary access. APIs must produce audit logging for data access, changes, and transmission. Hosting must use HIPAA-eligible cloud services, and vendors that create, receive, maintain, or transmit PHI on behalf of a covered entity need appropriate business associate agreement coverage.
HHS defines covered entities as health care providers, health plans, and health care clearinghouses, and HHS also states that business associates are directly liable for certain HIPAA provisions. HHS guidance on software vendors clarifies the practical rule for development partners: merely selling software does not create a business associate relationship, but hosting software containing patient information or accessing patient information for support can make the vendor a business associate.
Healthcare application development is therefore a specialized practice within custom web application development, and healthcare web application development services apply the same engineering discipline with an additional compliance architecture layer that non-regulated industries do not require. Mid-market healthcare organizations invest in custom healthcare applications when off-the-shelf healthcare software cannot support specific clinical workflow, patient engagement, integration, reporting, or specialty-care requirements.
HIPAA compliance shapes what healthcare applications look like, but the applications themselves serve four distinct operational needs.
Types of Healthcare Applications We Build
We build four types of HIPAA-compliant web applications for healthcare organizations:
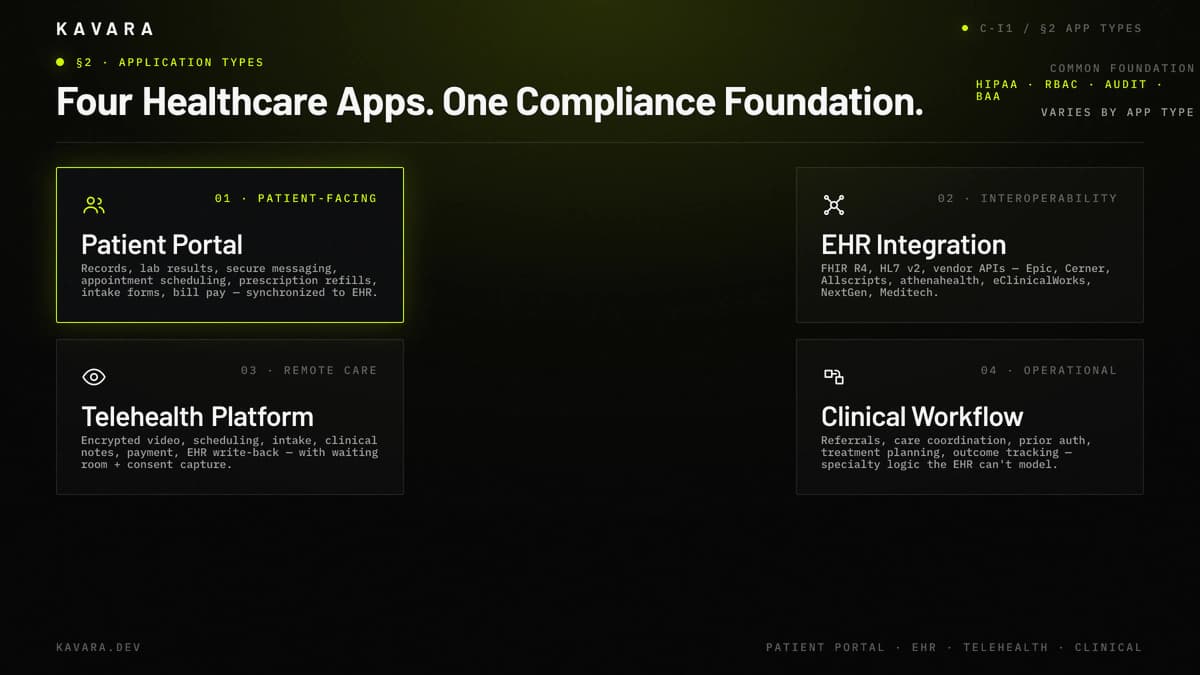
- Patient Portals - Patient portals are secure platforms where patients access records, view lab results, communicate with providers, manage appointments, request prescription refills, complete intake forms, and pay bills. Patient portal architecture requires HIPAA-compliant authentication, role-based access so each patient sees only their own data, encrypted messaging, and audit trails for every data access event. Integration with existing EHR systems is usually required so portal data stays synchronized with the clinical record. Patient portal development applies the same architecture principles as our broader enterprise portal development practice, with HIPAA-compliant authentication, role-based access, and encrypted communication layered on top.
- EHR Integration Platforms - EHR integration platforms connect to existing electronic health record systems such as Epic, Cerner, Allscripts, athenahealth, eClinicalWorks, NextGen, or Meditech through FHIR APIs, HL7 interfaces, and vendor-specific endpoints. EHR integration platforms extend EHR functionality without replacing the system of record. These platforms can add clinical decision support, patient-facing features, population health analytics, specialty workflow tools, or data synchronization that the core EHR does not natively support.
- Telehealth Applications - Telehealth applications support remote care through secure video consultation, scheduling, intake, encrypted messaging, clinical note capture, payment processing, and EHR update workflows. Telehealth development requires encrypted real-time communication, waiting room functionality, multi-party consultation support, consent capture, and compliant storage for session metadata or recordings when recording is part of the clinical workflow. Telehealth applications also need clear escalation paths when connectivity, identity verification, or clinical documentation fails.
- Clinical Workflow Tools - Clinical workflow tools support specialty-specific processes such as referral management, care coordination, patient intake, treatment planning, outcome tracking, prior authorization support, and operational reporting. Clinical workflow software often replaces paper-based, spreadsheet-based, or email-based processes that persist because the EHR cannot accommodate specialty-specific logic. These tools must preserve clinical context while reducing manual work and keeping PHI access scoped to the user's role.
All four application types share the same HIPAA architecture foundation: encrypted storage, role-based access control, audit logging, secure data transmission, and vendor review. Clinical workflow tools often include healthcare analytics dashboards for outcome tracking and department-level reporting, with data pipeline architecture and real-time visualization that healthcare operations require.
Every healthcare application type depends on the same compliance foundation: HIPAA architecture that protects patient data at every layer of the technology stack.
HIPAA Compliance Architecture
HIPAA compliance is not a feature added at the end of development. For custom web application development in healthcare, that requirement affects database encryption, API security, hosting configuration, and third-party integrations.
The architecture diagram below maps these controls across the UI, API, data, and infrastructure layers.
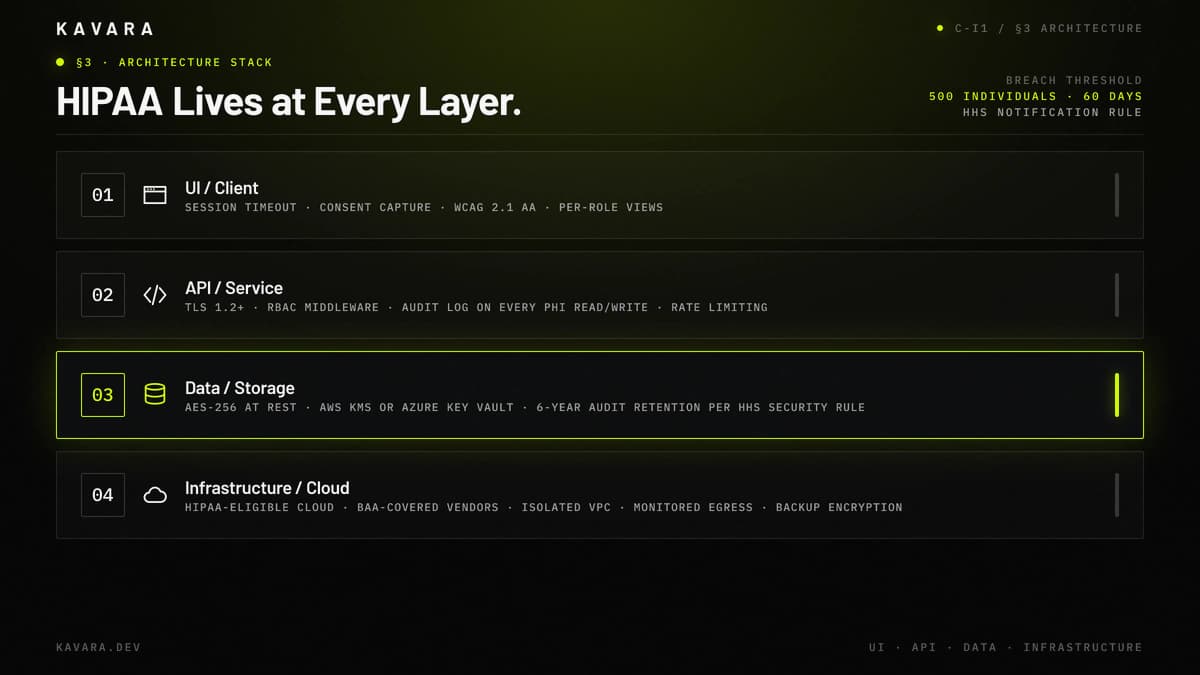
Data encryption protects stored and transmitted PHI. Production healthcare applications should use AES-256 at rest through AWS KMS or Azure Key Vault and TLS 1.2 or later in transit. HHS describes the Security Rule as requiring safeguards for the confidentiality, integrity, and availability of electronic protected health information, so HIPAA-compliant architecture treats databases, backups, logs, file uploads, and temporary processing locations as sensitive by default.
Access control defines which users can view, create, update, export, or administer PHI. Role-based access control maps patient, provider, nurse, administrator, billing, and care coordinator roles to data views and actions, enforcing minimum necessary access without universal administrator patterns.
Audit logging records activity in systems that contain or use electronic PHI. HHS Security Rule guidance identifies audit controls as technical safeguards and points to mechanisms that record and examine activity in systems containing electronic PHI. A healthcare application should log user identity, timestamp, action performed, record accessed, and administrative changes; HHS also states that Security Rule documentation must be retained for six years from creation or last effective date.
Transmission security protects PHI as it moves between browsers, APIs, EHR systems, and third-party services. Healthcare applications should use HTTPS/TLS for APIs, encrypted messaging, secure upload handling, and controlled outbound rules so PHI does not move through standard email, unencrypted exports, or logging systems without HIPAA-eligible controls.
BAA coverage completes the architecture boundary. HHS cloud guidance allows cloud providers for electronic PHI when safeguards and business associate agreements are in place, so every infrastructure, analytics, messaging, video, or support tool that handles PHI needs BAA review. HIPAA security requirements build on our broader web application security best practices framework with healthcare-specific controls layered on top.
Breach notification readiness also belongs in the architecture. HHS states that breaches affecting 500 or more individuals must be reported no later than 60 calendar days from discovery, so healthcare applications should support incident detection, access investigation, affected-record identification, and notification evidence.
Compliance architecture determines how the application handles data internally, but healthcare applications also need to exchange data with external systems using healthcare-specific interoperability standards.
Healthcare Data Integration and Interoperability
Healthcare applications rarely operate in isolation: portals pull data from EHRs, clinical tools push results back, and telehealth sessions create clinical records. Healthcare interoperability - reliable, secure exchange between systems - is an architecture requirement rather than an optional integration.
The integration topology below shows how a HIPAA-compliant application connects to Epic, Cerner, Allscripts, athenahealth, and HL7 v2 legacy systems.
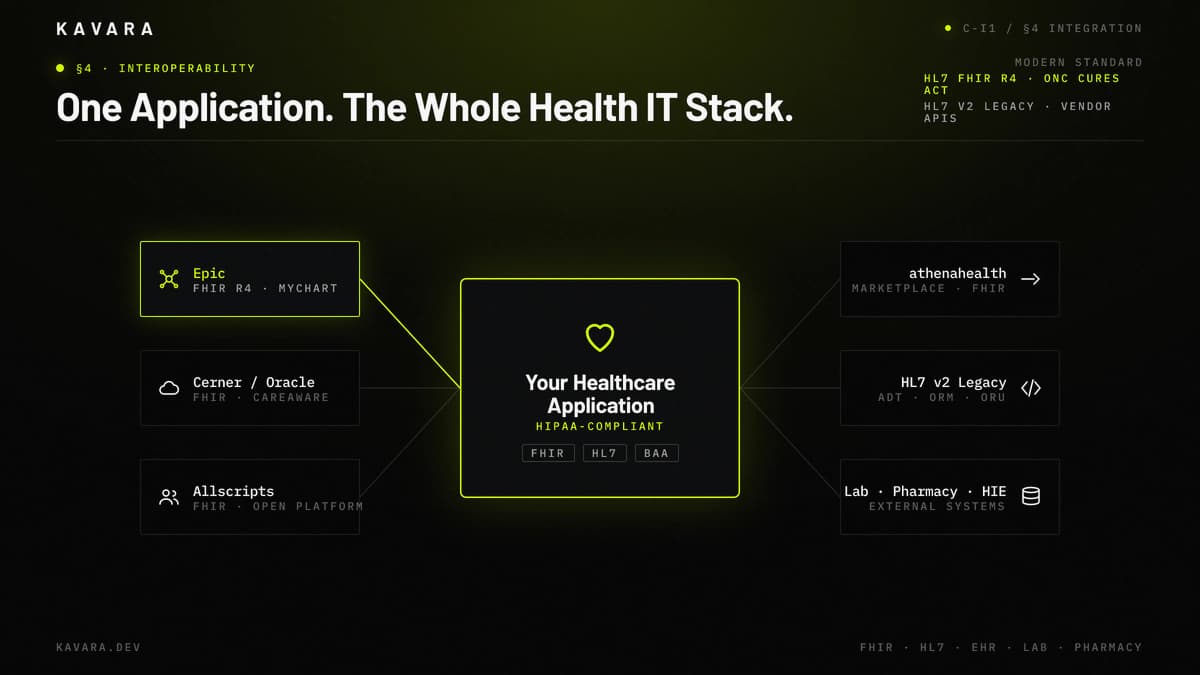
FHIR, or Fast Healthcare Interoperability Resources, is the modern standard for healthcare data exchange. ONC describes HL7 FHIR as a widely used open standard based on modern internet technology and notes that FHIR was incorporated into the Health IT Certification Program for the 21st Century Cures Act. FHIR uses API-based resources such as Patient, Observation, Encounter, and DiagnosticReport so healthcare applications can exchange clinical data through standardized structures.
The 21st Century Cures Act changed the integration baseline for certified health IT systems. ONC states that the Cures Act Final Rule supports patient and provider access to electronic health information through HL7 FHIR APIs, and ONC data briefs note that certified EHR users must have standardized FHIR APIs available for authorized exchange. For custom healthcare application development, EHR integration strategy increasingly starts with FHIR endpoints before falling back to older interface patterns.
HL7 v2 is the legacy healthcare messaging standard still used by many hospital systems and older EHR integrations. Its ADT, ORM, and ORU messages require parsing, transformation, and interface engine configuration. EHR integration projects must handle both modern FHIR APIs and older HL7 interfaces depending on the health system's infrastructure.
EHR-specific APIs add another layer. Epic, Cerner, athenahealth, Allscripts, and other vendors provide proprietary APIs, sandbox environments, production credentialing, and platform-specific approval processes, so integration timelines depend on vendor access as much as engineering work.
Data mapping preserves clinical meaning across systems. Healthcare data uses ICD-10 for diagnoses, CPT for procedures, LOINC for labs, and SNOMED CT for clinical terms. Integration platforms must map and transform data carefully so clinical accuracy survives movement between EHRs, portals, billing systems, labs, pharmacies, and health information exchanges.
Building applications with this compliance and integration architecture requires a development process adapted for healthcare-specific requirements at every phase.
Our Healthcare Development Process
We build healthcare applications through our structured development process with compliance requirements addressed at every phase:
- Discovery - Discovery identifies covered entity and business associate obligations, maps PHI data flows, documents compliance requirements, scopes EHR integration, reviews BAA needs, and defines the clinical workflow problem the application must solve.
- Design - Design covers HIPAA-compliant user flows, session timeout behavior, consent capture, patient-provider messaging patterns, WCAG 2.1 AA accessibility expectations, and clinical workflow mapping with provider input.
- Architecture - Architecture defines PHI encryption strategy, RBAC schema design, audit logging architecture, HIPAA-eligible cloud configuration, integration interface design, backup strategy, and FHIR or HL7 data exchange patterns.
- Development - Development implements encryption, access control, audit trails, secure messaging, EHR sandbox integration, PHI boundary controls, and healthcare-specific validation rules.
- QA - QA verifies HIPAA security controls, PHI access boundaries, role-based permissions, audit trail coverage, data mapping accuracy, penetration test findings, and compliance documentation.
- Deployment - Deployment uses HIPAA-eligible infrastructure, verifies BAA coverage for third-party services, confirms security configuration, and prepares monitoring for application health, access anomalies, and integration failures.
- Support - Support includes security patching, EHR integration maintenance, annual risk assessment support, audit log review support, incident response readiness, and updates when vendor APIs or clinical workflows change.
Our healthcare development methodology follows our structured development process with HIPAA compliance requirements addressed at every phase, from risk assessment in discovery through security testing in QA.
Healthcare application development investment reflects the compliance architecture, integration complexity, and specialized testing that regulated applications require.
How Much Does Healthcare Application Development Cost
Healthcare application development typically costs 20% to 40% more than equivalent non-regulated applications due to HIPAA compliance architecture, security testing, and EHR integration requirements. The compliance premium comes from encrypted infrastructure, role-based access control, audit logging, penetration testing, BAA management, documentation, and PHI-specific QA.
Patient portals with EHR integration usually sit in the upper range of portal development cost, often $150,000 to $300,000 depending on EHR complexity, messaging, scheduling, payments, and record access. Telehealth platforms usually cost $150,000 to $350,000 when secure video, scheduling, intake, clinical notes, payment, and EHR integration are included. Clinical workflow tool costs depend on scope, and mid-complexity applications often cost $100,000 to $250,000 based on user roles, workflow logic, integrations, and reporting depth.
Ongoing healthcare application costs include HIPAA risk assessment updates, penetration testing, security monitoring, hosting, incident response preparation, vendor review, and EHR integration maintenance. Annual HIPAA risk assessment support and penetration testing can each add $5,000 to $15,000 depending on scope.
Healthcare projects should be estimated against the base application type first, then adjusted for compliance and integration complexity. For detailed cost ranges across all application types and the compliance premium that healthcare projects carry, see our web application development cost guide.
What Is HIPAA and How Does It Affect Application Development
HIPAA, the Health Insurance Portability and Accountability Act, is a US federal law governing how protected health information is collected, stored, accessed, used, disclosed, and transmitted. Any healthcare application that handles PHI must account for HIPAA's technical safeguards, including access control, audit controls, integrity controls, person or entity authentication, and transmission security.
Access control verifies who can use PHI, audit controls record activity, integrity controls protect data from improper alteration, and transmission security protects PHI in motion. HIPAA applies to covered entities and business associates. Covered entities include health care providers, health plans, and health care clearinghouses. Business associates include vendors that create, receive, maintain, or transmit PHI on behalf of covered entities. HHS states that civil money penalty caps are adjusted annually and that its Privacy Rule summary lists calendar-year caps from $25,000 to $1,919,173 for identical requirements or prohibitions under OCR enforcement discretion. Compliance is therefore an architecture requirement from discovery, not an aftermarket feature.
How Long Does Healthcare Application Development Take
Healthcare application development typically takes 4 to 10 months from discovery to launch, or about 20% to 30% longer than equivalent non-regulated applications, due to compliance architecture, security testing, and EHR integration credentialing. A patient portal with EHR integration usually takes 4 to 7 months. A telehealth platform usually takes 5 to 8 months. A complex clinical workflow tool usually takes 6 to 10 months.
The primary timeline factors are EHR vendor credentialing, HIPAA security testing, PHI access boundary verification, and clinical stakeholder review. EHR credentialing can add 4 to 8 weeks when vendor sandbox access, production approval, or interface engine configuration is required. Projects with multiple EHRs, specialty workflows, or clinical stakeholder review cycles trend toward the upper end of the range.
What Healthcare Systems Can Custom Applications Integrate With
Custom healthcare applications integrate with major EHR and EMR platforms through FHIR APIs, HL7 interfaces, and vendor-specific integration endpoints:
- Epic - FHIR R4 APIs and MyChart integration patterns.
- Cerner / Oracle Health - FHIR APIs and CareAware ecosystem integration.
- Allscripts - FHIR APIs and open platform integration.
- athenahealth - Marketplace APIs and FHIR endpoints.
- eClinicalWorks, NextGen, and Meditech - HL7 v2 interfaces and vendor APIs.
Integration also extends to pharmacy systems, lab information systems, medical billing platforms, insurance verification services, and health information exchanges. Healthcare applications increasingly embed clinical decision support, document processing, and predictive analytics through our AI implementation services, with HIPAA-compliant data pipeline architecture.
How to Choose a Healthcare Application Development Partner
Evaluate a healthcare development partner on five criteria beyond standard software evaluation:
- HIPAA expertise demonstrated through architecture decisions, not compliance claims.
- EHR integration experience with the platforms your organization uses.
- Healthcare domain knowledge for clinical workflows, not generic portals.
- Security testing methodology covering penetration testing, PHI boundary verification, and compliance documentation.
- BAA willingness because the partner may be a business associate when handling PHI.
A development partner who treats HIPAA as a final checklist creates regulatory and security risk. Beyond healthcare-specific criteria, the general evaluation framework in our guide to choosing a development company covers process transparency, team composition, technical diligence, and post-launch support. These criteria turn the architecture requirements above into a partner-selection standard for a compliant build.
Next Steps
Healthcare application development helps mid-market healthcare organizations build, launch, and comply with HIPAA requirements for patient portals, EHR integration platforms, telehealth applications, and clinical workflow tools. These healthcare development services build web applications with encrypted data storage, role-based access control, audit logging, secure transmission, and BAA-aware vendor selection. Most healthcare projects carry a 20% to 40% compliance premium and take 4 to 10 months because HIPAA architecture, security testing, and EHR credentialing add work before launch. Explore our full custom web application development services to see how healthcare applications connect to our SaaS, portal, dashboard, and enterprise software practices. Contact Kavara to assess compliance requirements, map EHR integration needs, and scope your healthcare application build.